SwarmSim
Model your facility edge and expose readiness gaps before procurement.
- ✓High-fidelity site modeling and digital twins
- ✓Approved defensive scenario simulation
- ✓Validate controls and reduce coverage gaps
Counter-drone readiness software
CounterSwarm helps critical infrastructure, defense consultants, and government-readiness teams model drone exposure, pressure-test defensive workflows, preserve evidence, and generate board-ready readiness outputs.
Quick answer
CounterSwarm is built for teams that need a credible defensive readiness baseline before they commit to broader procurement, integration, or program funding. That includes defense consultants, government-readiness teams, and critical-infrastructure operators.
Proof snapshot
CounterSwarm publishes machine-readable proof, explicit non-claims, and a buyer-facing capability boundary so consultants and partner teams can cite the current software truth without guessing.
Product overview
CounterSwarm brings site modeling, scenario simulation, report generation, and response workflow into one workspace for defense, government-readiness, and critical-site teams.
Model your facility edge and expose readiness gaps before procurement.
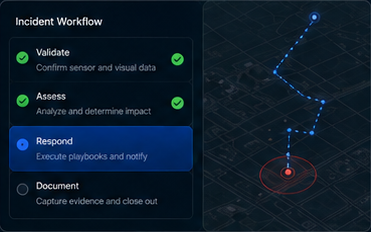
Operator-ready next steps for incidents — without the guesswork.
Extend into staged operator context across sensors and sites.

From site context to a buyer-reviewable readiness output in 48 hours.

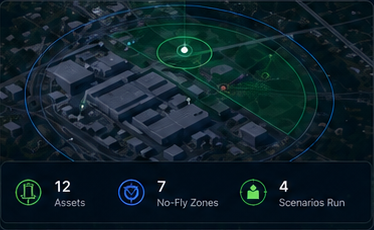
Model assets, airspace, zones, and workflow assumptions around the facility edge.

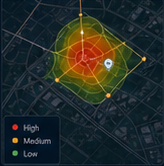
Use defensive-only scenarios to expose coverage, process, and response gaps.

Get scores, prioritized gaps, remediation priorities, and downloadable report outputs.

Operationalize evidence handling, track actions, and leave with a concrete next-step decision.
Board-ready by design
Board-ready reports with scores, gaps, remediation priorities, and evidence trails — packaged for operators, advisors, and procurement.
View report sample
Designed for infrastructure, defense-sensitive facilities, and operators who need disciplined readiness before procurement.
Identify vulnerabilities, drill scenarios, and train response teams — before an incident occurs.
Assessments are framed for security leaders who need defensible findings, remediation priorities, and a clear operating record.
We don't provide active countermeasures, defeat-system recommendations, or command-and-control claims.
Early access · limited cohort
Run a focused pilot that documents site exposure, evidence workflow, and remediation priorities before larger procurement decisions.